
Mario P. Fucinari DC, CCSP, CPCO, MCS-P, MCS-I
Under HIPAA, the patient must have access to their records in a timely manner. A drawback in the increased use of Electronic Health Records (EHR) is that cybercriminals may hack into a patient’s records or malware may infiltrate your system, impeding access to the records. One such cybercriminal threat is through “ransomware” attacks on healthcare professionals’ computer systems, putting private patient health information (PHI) at risk.
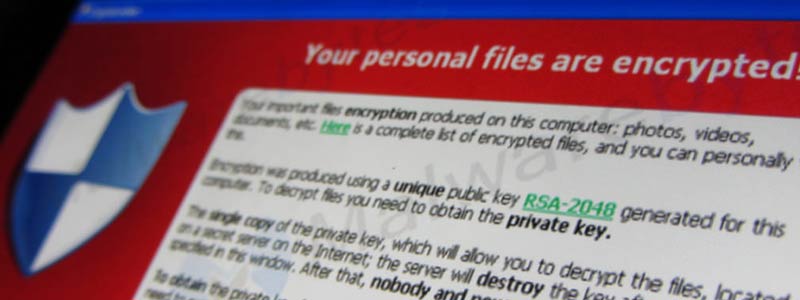
Ransomware attacks begin when a cybercriminal sends a healthcare professional an eye-catching email link to contagious attachments. Once a person clicks on a link and downloads the attachment, the computer’s information becomes encrypted and frozen with malware. A “ransom note” then appears on the computer screen demanding the user pay a ransom in exchange for a key code to unlock the data.
Since early 2016, there have been an average of 4,000 daily ransomware attacks (a 300 percent increase over the 1,000 daily ransomware attacks reported in 2015).1 An estimated half a billion dollars has been paid ransom, usually by bitcoin. In February 2016, Hollywood Presbyterian Medical Center in California revealed that they paid hackers a ransom in bitcoin amounting to the equivalent of $17,000.2
Here are tips to avoid a ransomware attack (or at least minimize its damage if an attack is in process or has occurred):
- Back up your most important files regularly and periodically review the backup to ensure its integrity and completeness. Some forms of ransomware will remove, encrypt or disrupt backups even in the Cloud. Consider maintaining any backups offline, away from any networks.
- Personalize your anti-spam settings. Configure your webmail server to block dubious attachments with extensions like .exe, .vbs or .scr.
- Refrain from opening attachments that look suspicious. Phishing emails may masquerade as notifications from a delivery service, an e-commerce resource, a law enforcement agency or a banking institution.
- Think twice before clicking. Dangerous hyperlinks can come through social networks or instant messages. Senders may be using hacked accounts to appear as people you trust, including friends or colleagues.
- Patch and keep your operating system and software up to date to help prevent compromise via exploit kits. This includes antivirus, browsers, Adobe Flash Player and Java.
- If you spot a suspicious process on your computer, instantly turn off the internet connection. This may stop the ransomware from completing the encryption routine.
- Keep the Windows firewall turned on and properly configured. Enhance your protection by setting up additional firewall protection. Third-party security suites are available that to enhance the security already built into Windows.
- Adjust your security software to scan compressed or archived files.
- Use strong passwords that cannot be brute-forced by remote criminals. Set up unique passwords for different accounts.
- Deactivate auto play so harmful processes won’t be automatically launched from external media, such as USB memory sticks or other drives.
- Disable file sharing to keep any ransomware infection isolated to your machine.
- Switch off unused wireless connections, such as Bluetooth or infrared ports. Bluetooth has been exploited to stealthily compromise systems.
- Block known-malicious Tor IP addresses. Tor (The Onion Router) gateways are the primary means for ransomware threats to communicate with their command and control servers. Therefore, blocking Tor may impede critical malicious processes.
At times, it may seem difficult to stay up to date with the latest cybercrimes, but due diligence through a risk analysis is critical. According to information technology experts, the next generation of ransomware includes the threat of leaking the information if payment is not made, thus a greater HIPAA violation. Remember to conduct a risk analysis, consult with an IT specialist and document all your efforts.
- United States Government Interagency Guidance Document, How to Protect Your Networks from Ransomware available at https://www.justice.gov/criminal-ccips/file/872771/download
- Ransomware takes Millions, Baffles Law Enforcement, http://thehill.com/policy/cybersecurity/270097-ransomware-takes-millions-baffles-law-enforcement
Mario Fucinari, D.C., CCSP, MCS-P, CPCO, is in private practice in Decatur, Illinois. He is a Certified Medical Compliance Specialist and a Certified Professional Compliance Officer. He is a frequent lecturer and is on the NCMIC and Foot Leveler’s speakers bureau. For speaking at state conventions or audit services, contact Dr. Fucinari at Doc@Askmario.com.










 Why is the Discount Challenge prize amount $11,181? Because that is the average “per-occurrence” fine for Medicare inducements. That’s not $11,181 per patient, that’s not per provider, that’s PER VISIT. Stinks, doesn’t it? To us, the prize amount is worth the investment if we can help our profession better understand proper discounting.
Why is the Discount Challenge prize amount $11,181? Because that is the average “per-occurrence” fine for Medicare inducements. That’s not $11,181 per patient, that’s not per provider, that’s PER VISIT. Stinks, doesn’t it? To us, the prize amount is worth the investment if we can help our profession better understand proper discounting.